Is your google account hacked? Over 1 million google accounts have been compromised till now!

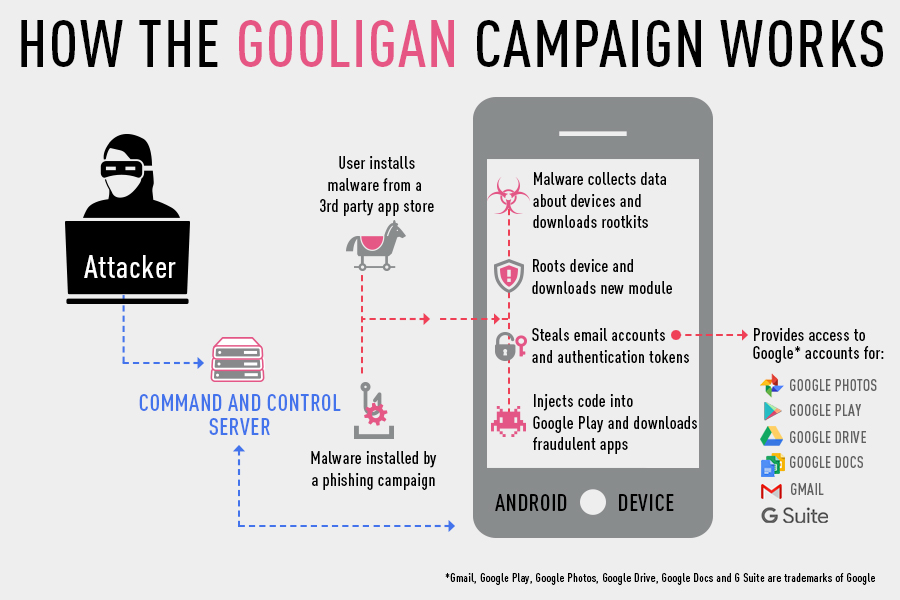
Gooligan is an Android Malware that infects and compromised Google accounts. The malware steals authentication details and can access Google apps including Gmail, Google Photos, Google Docs, Google Play, Google Drive etc.
How does Gooligan work?
The infection begins when a user:



My device is infected, now what?
How to stay safe?
If you do doubt that you may be infected and compromised, you can enter in your email on a website created by Check Point for the same purpose. Google’s Director of Android Security, Adrian Ludwig, points to Check Point’s blog in his Google+ post, as Check Point has been working closely with Google to understand the issue.






Follow Us