WannaCry (WCRY) Ransomware Protection for end users and Organizations
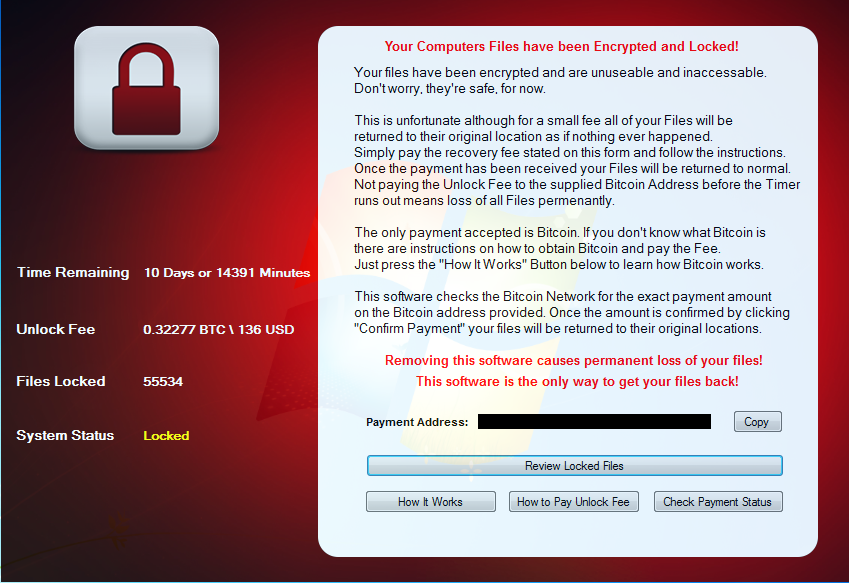
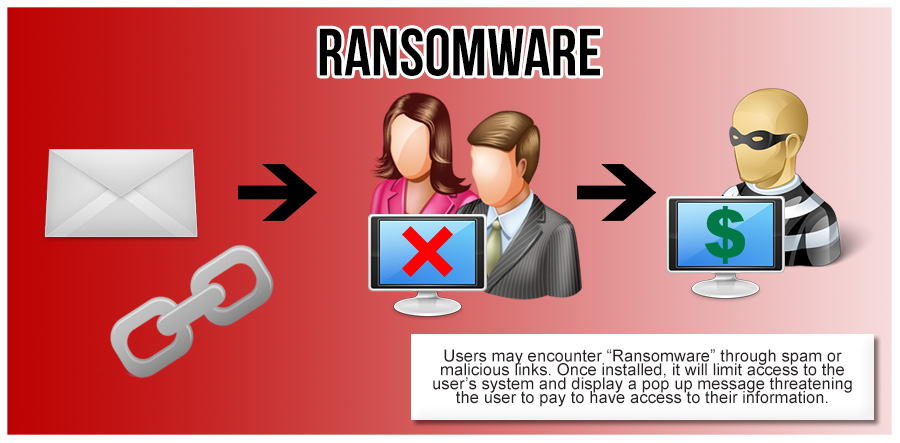
WannaCry (WCRY) Ransomware is serious threat to business, it is a special kind of virus used by hackers to lock access to important files on user’s computers; and they ask for money to unlock the files again. Cyber extortionists trick victims into opening malicious malware attachments to spam emails that appeared to contain invoices, job [...]