Get compliant with PCI, HIPAA, GDPR, FedRAMP, SOC 2 by cloud services of AWS, GCP and Azure
This article provides guidance on how to get your business compliant with PCI, HIPAA, GDPR, FedRAMP, SOC 2 by leveraging cloud services of AWS, GCP and Azure. Organizations providing IT Managed Services, Software Development, Software as a Service, infrastructure-as-a-service, platform-as-a-service tend to have their application products hosted on the cloud [...]
SOC 2 Audit Controls and Checklist
The AICPA Assurance Services Executive Committee (ASEC) has developed a set of criteria (trust services criteria) to be used when evaluating the suitability of the design and operating effectiveness of controls relevant to the security, availability, or processing integrity of information and systems, or the confidentiality or privacy of [...]
Illustrative Examples for SOC 2 certification
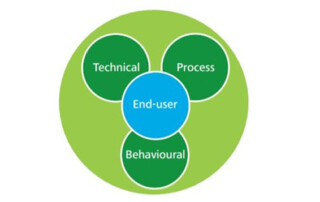
Is your client information and data safe? How will you assure it? Two very important questions for which you should have very clear answers if you offer IT services to your clients. If you are an IT service organization you must meet your clients’ great demands for the security of their data. [...]
The cost of SOC 2 Certification services
Today, more than ever, organizations need to ensure the security, availability, privacy, processing integrity and confidentiality of their data and underlying systems—regardless of whether they managed are in-house or outsourced. E Com Security Solutions's Information & Controls Assurance practice specializes in detecting risks that affect internal systems, business processes, projects, [...]
How to validate compliance with PCI DSS standard
PCI DATA SECURITY STANDARD The PCI Data Security Standard requirements apply to all payment card network members, merchants, and service providers that store, process or transmit cardholder data. The core requirements are organized into six categories: Build and Maintain a Secure Network 1. Install and maintain a firewall configuration to [...]