Vulnerability Management
E Com Security Solutions offers the expertise of highly skilled security professionals to help organizations identify vulnerabilities. Our team works shoulder to shoulder with organizations to remedy and manage these vulnerabilities.
A comprehensive solution for vulnerability management
Businesses rely on a stable and secure IT environment as the foundation for driving new digital innovations and products. New security vulnerabilities are published on a daily basis and hackers are constantly looking for ways to gain access to systems and data. Identifying, managing and correcting vulnerabilities in an environment that consists of multiple applications, systems and locations is a significant management challenge.
Our services include fully managed vulnerability assessments from E Com Security Solutions’ award-winning ethical hackers and support in designing, implementing and operating vulnerability-management systems and processes. We offer a range of managed solutions including vulnerability assessments, remediation support and vulnerability management advisory.
Adopt a vulnerability management program that identifies, prioritizes and manages the remediation of flaws that can expose your most-critical assets.
Vulnerabilities and remediation management
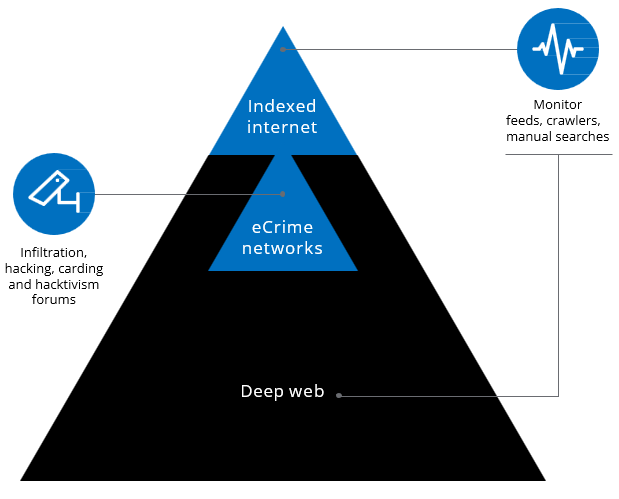
Organizations must begin approaching vulnerability management as a multistep process, not a one-time scanning effort. Based on the sheer number of existing and new vulnerabilities, an effective program will focus the organization’s efforts on the highest-risk vulnerabilities
in an ongoing fashion.
Given that many organizations may have millions of vulnerabilities, many of which expose highly sensitive assets, the need for prioritization and efficient remediation is evident. E Com Security Solutions’ Vulnerability Management Services use attacker-minded expertise and algorithms to help organizations build a more efficient, effective vulnerability management program. The result can help organizations save time and resources and, most importantly, minimize the risk of compromise.
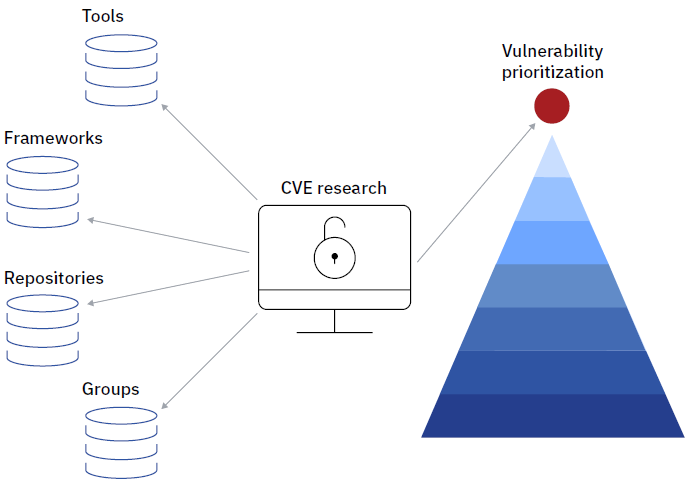

Vulnerability Management Capability Design
E Com Security Solutions helps organizations establish VM processes, governance, capabilities, tools, and expertise. We help organizations identify, manage, and resolve issues with stakeholders in a timely way.
We validate vulnerabilities that can be overlooked, such as input errors when data comes from untrusted sources, is purposefully or incorrectly entered, which can lead to attacks, and then present vulnerability management research and findings to your executive team, in their language. This helps generate executive-level support for prioritizing and patching critical vulnerabilities.
Innovate with Confidence
The data shows why E Com Security Solutions is the right partner for your cyber defense strategy.
Resources to help you drive compliance and speed within your enterprise.
Breaking the Black Box: LLM Penetration Testing, Attack Simulation & Model Landscape
LLM Penetration testing and Attack simulation With their growing use across industries, security teams need to carefully assess these models for potential risks. By examining threats like prompt injection, data [...]
AI Impact Assessment Process
The nomenclature around AI impact assessments and its relationship to other evaluations of AI are unsettled. Some Organizations use “AI risk assessment” and “AI impact assessment” interchangeably, while others distinguish [...]
Vulnerability Response Playbook
One of the most straightforward and effective ways for an organization to prioritize vulnerability response and protect from being compromised is by focusing on vulnerabilities already being actively exploited in [...]