Security Operations Center (SOC)
With 24/7 SOC capabilities, advanced incident forensics, AI-driven threat intelligence, and industry-leading practices to enable continuous monitoring, rapid detection, and autonomous response.
AI-Powered Threat Detection and Response
Powering the future of security operations centers, our solutions fortify your business and IT ecosystem against emerging cyber threats by leveraging cutting-edge technological advancements, AI-driven threat intelligence, and industry-leading practices to deliver continuous monitoring, rapid detection, autonomous response, and advanced incident forensics—supported by 24/7 managed or on-premise SOC capabilities and the expertise to architect next-generation, proprietary security operations.
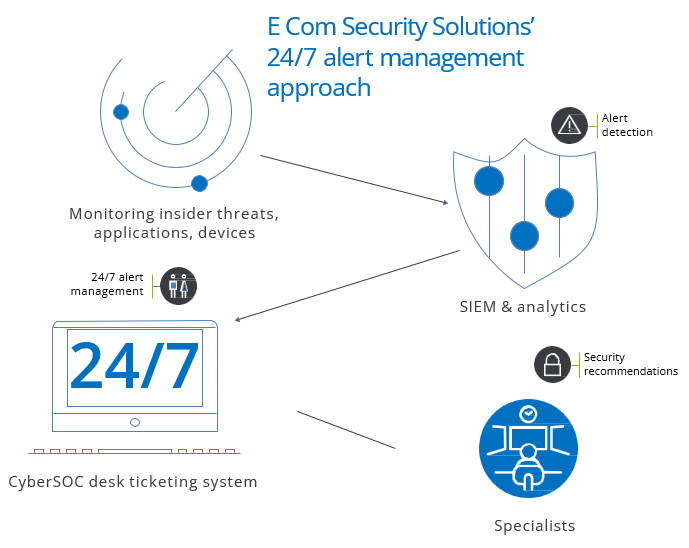
Managed SOC services, on-site and hosted, which integrate event monitoring and correlation with threat intelligence and
a business-focused output
Threat intelligence and analysis
Our solutions prepare organizations’ IT landscape and security operations for evolving risks and future cyber threats. Our security operations center (SOC) service offering leverages the latest technology, leading practices, and world-class threat intelligence to enable rapid monitoring, containment, and response to evolving cyber threats.
In the event of a cyber incident, our forensic specialists take rapid action to investigate and contain the situation. We provide monitoring and analytics that deliver actionable intelligence, enabling you to proactively protect against threats before they arise. Our AI capabilities helped reduce low-value SIEM alerts by 45% and auto-escalate 79% more high-value alerts requiring immediate attention.
MITRE ATT&CK optimization
To stay prepared for ransomware and wipe-out attacks, organizations can see how their environment covers MITRE ATT&CK framework tactics, techniques, and procedures compared to their industry and geographic peers.
By applying AI, the E Com Security Solutions’ SOC services are designed to reconcile the multiple detection tools and policies currently in place at an organization, providing an enterprise view into how to best detect threats and assess gaps to update within an ATT&CK framework.
Innovate with Confidence
The data shows why E Com Security Solutions is the right partner for your cyber defense strategy.
Resources to help you drive compliance and speed within your enterprise.
Breaking the Black Box: LLM Penetration Testing, Attack Simulation & Model Landscape
LLM Penetration testing and Attack simulation With their growing use across industries, security teams need to carefully assess these models for potential risks. By examining threats like prompt injection, data [...]
AI Impact Assessment Process
The nomenclature around AI impact assessments and its relationship to other evaluations of AI are unsettled. Some Organizations use “AI risk assessment” and “AI impact assessment” interchangeably, while others distinguish [...]
Vulnerability Response Playbook
One of the most straightforward and effective ways for an organization to prioritize vulnerability response and protect from being compromised is by focusing on vulnerabilities already being actively exploited in [...]